Executive Summary#
Castle’s Research Team continues to monitor the evolving bot landscape, with this report providing a comprehensive analysis of BotmasterLabs, a software company known for developing spam-related tools that have gained adoption in both the Russian and Western cybercrime spaces. BotmasterLabs is known for XRumer, a forum spamming toolkit, and XEvil, a CAPTCHA-solving plugin, both of which have enabled low-level spam for the past decade. XRumer grants clients the ability to import or select predefined lists of websites to spam with custom messages, and it has been observed being used to push malvertising or pharmaceutical-based advertisements. This software is provided in addition to XEvil and leverages both Optical Character Recognition (OCR) and machine learning models to solve over 100 different text- and image-based CAPTCHAs.
Defenders should use and enforce strict browser fingerprinting techniques and apply additional scrutiny to IPv6 and Datacenter IP ranges. Additionally, organizations should use multiple forms of challenge and not over-rely on a single form of verification; instead, use a holistic analysis of the user beyond a single fingerprint, IP address, or email.
Looking ahead, Castle’s Research Team expects continued adoption of third-party tools to power large-scale bot farms and credential-stuffing attacks. XEvil highlights the significant shortcomings of image-based CAPTCHA, suggesting the need for more complex signals.
Background#
BotmasterLabs is a Russian-speaking actor that has been operating since early 2007, and it is best known for developing XRumer, one of the largest forum-spamming toolkits, and XEvil, a CAPTCHA-solving plugin used for low-level credential stuffing and large-scale account farms. This software has gained popularity due to its low barrier to entry in both cost and skill, making it an easy choice for circumventing traditional security measures. Castle’s Research Team continues to track the CAPTCHA and spam ecosystem to protect clients and build stronger client-side fingerprinting signals for automated abuse. This report aims to provide a comprehensive analysis of the techniques, tactics, and procedures (TTPs) used by both tools, with findings highlighting significant shortcomings that enable defenders to detect and mitigate automated abuse.

XRumer is one of the first products offered by BotmasterLabs, marketed as a “link-building tool” that could automatically register accounts on various forum software and promote custom-made messages. XRumer would gain early adoption among spammers, used for a wide range of purposes, from pushing malvertising to running pharmaceutical ads. Since its initial release, the software has undergone significant improvements, with the latest release introducing AI for content generation and form detection, as well as improvements to anti-bot circumvention.
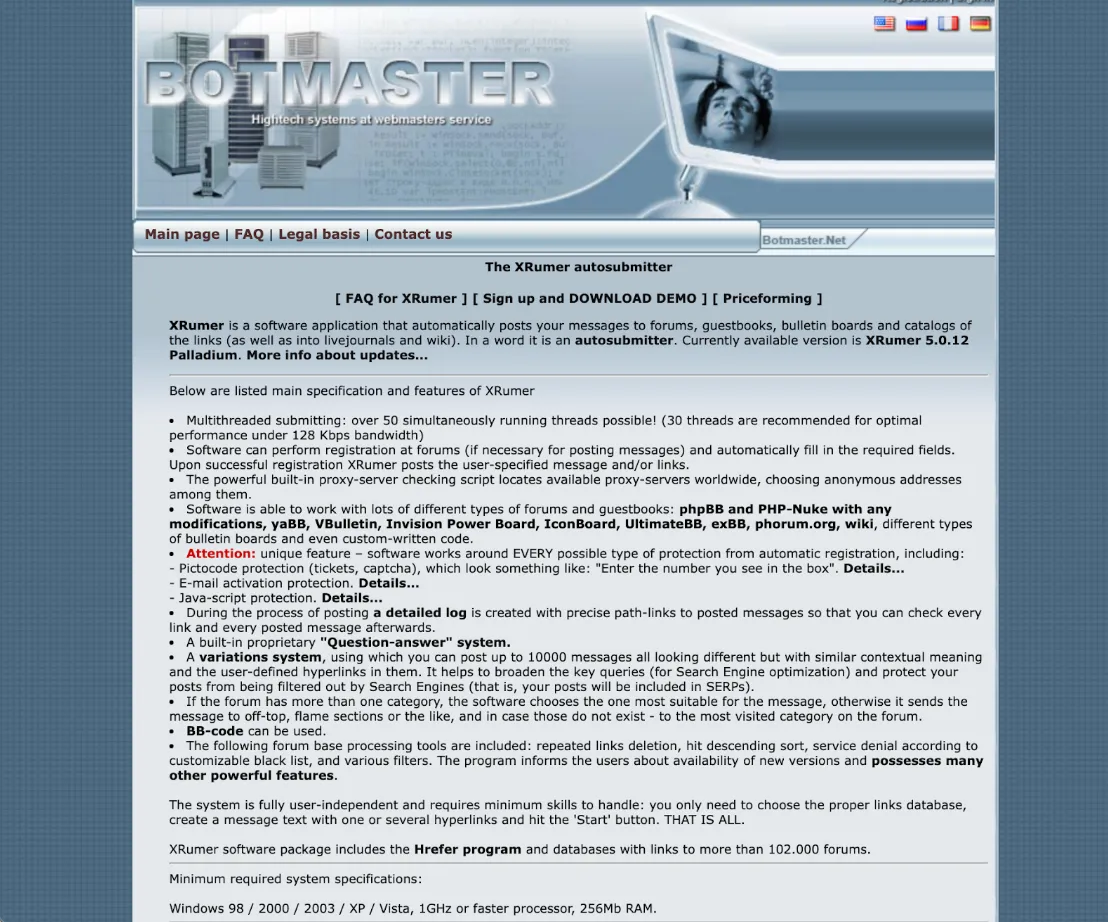
In addition to gaining access to the software, BotmasterLabs clients receive ~20 million links to various forums and websites that can be used immediately in XRumer to spam with custom messages. Clients can also use BotmasterLabs HRefer to find new links for forums, guestbooks, blogs, and Wikis.
XRumer Analysis#
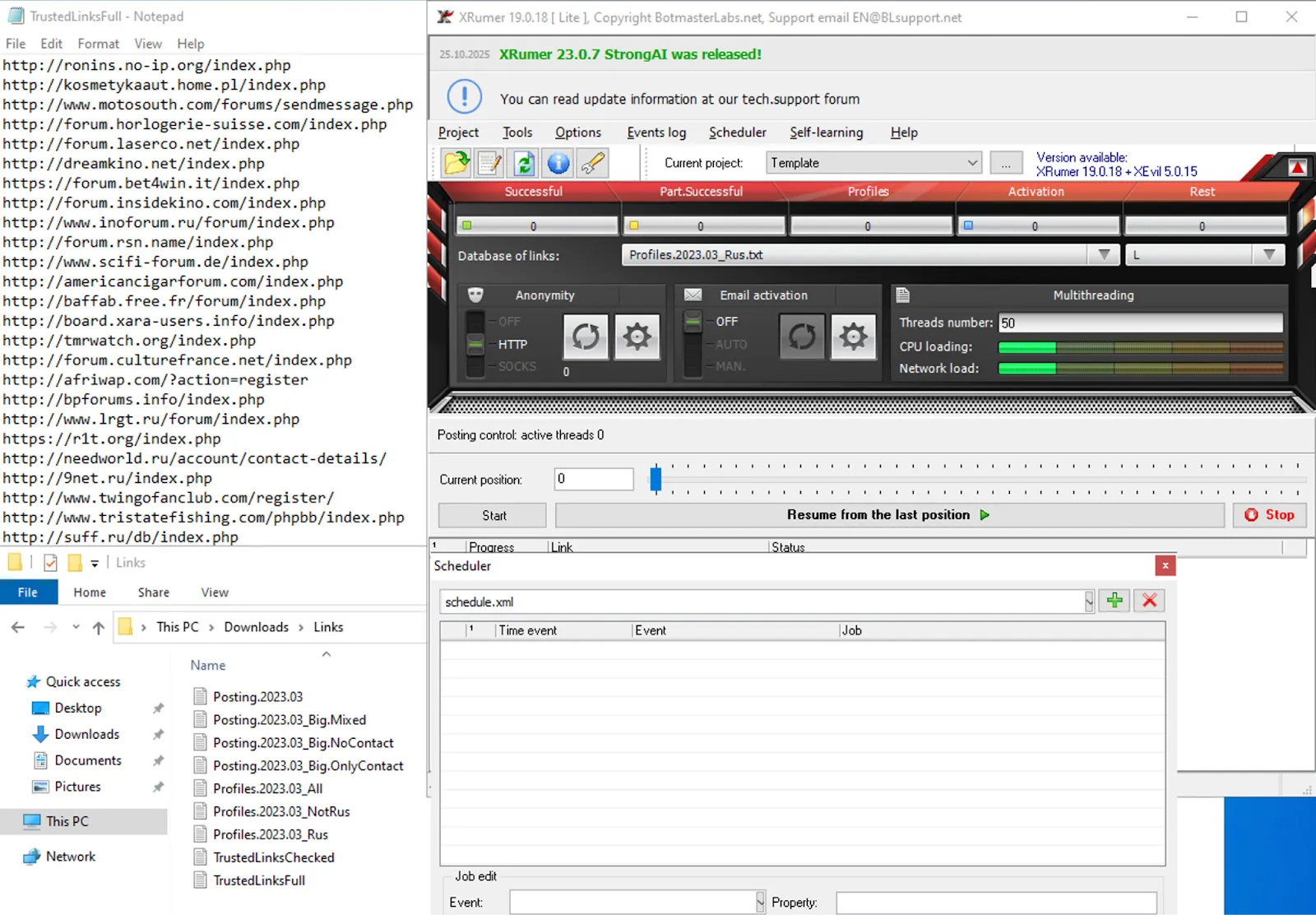
XRumer provides a user-friendly graphical interface, allowing users to configure everything from the messages sent to the user details for registered accounts. XRumer provides an additional set of text files containing realistic, random information for use in campaigns. Users can select a specific theme and further fine-tune randomized content around it. Users can also configure proxies, custom rules, scheduling, and self-learning to circumvent bot-protection measures and appear more realistic.
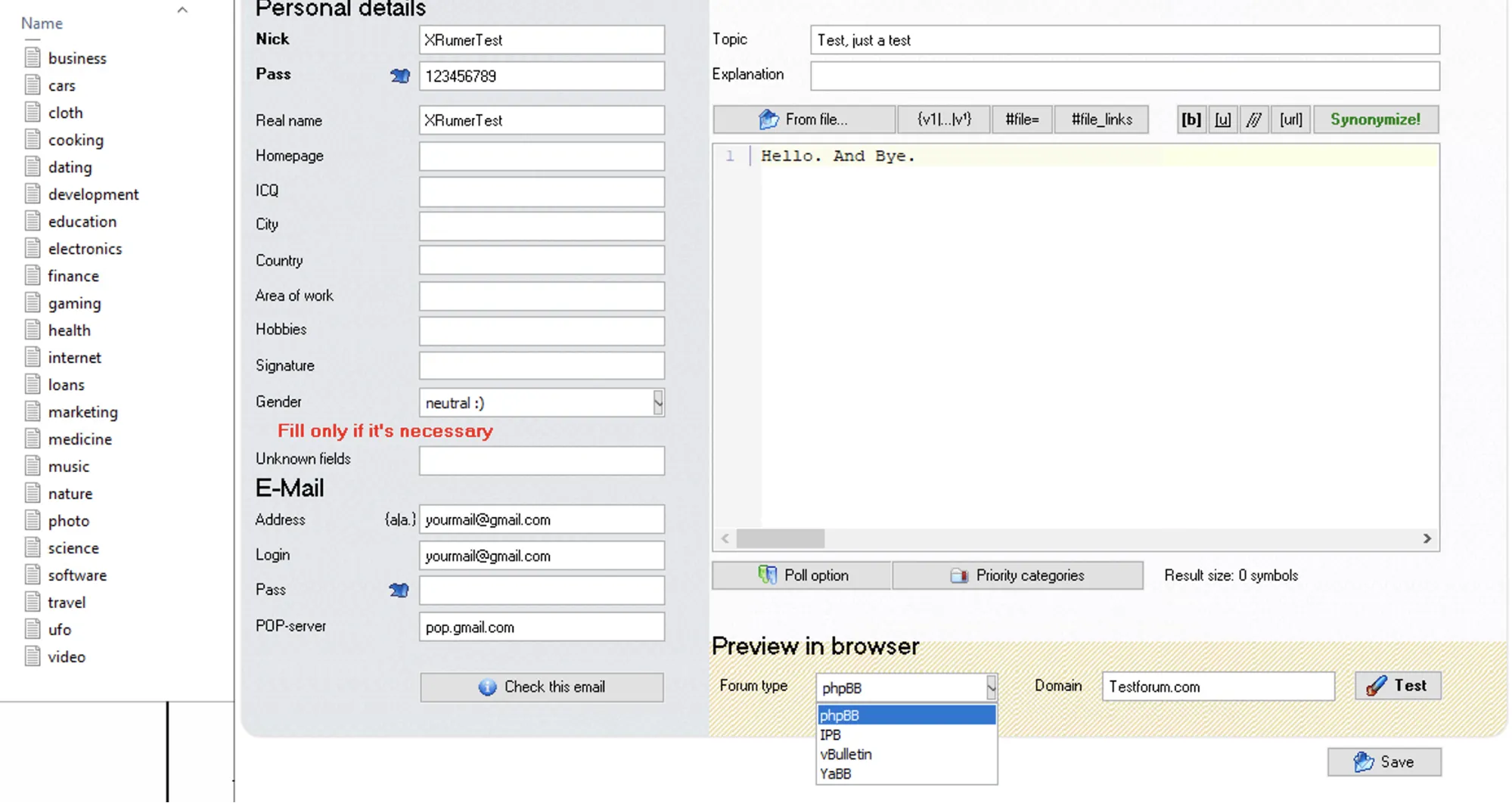
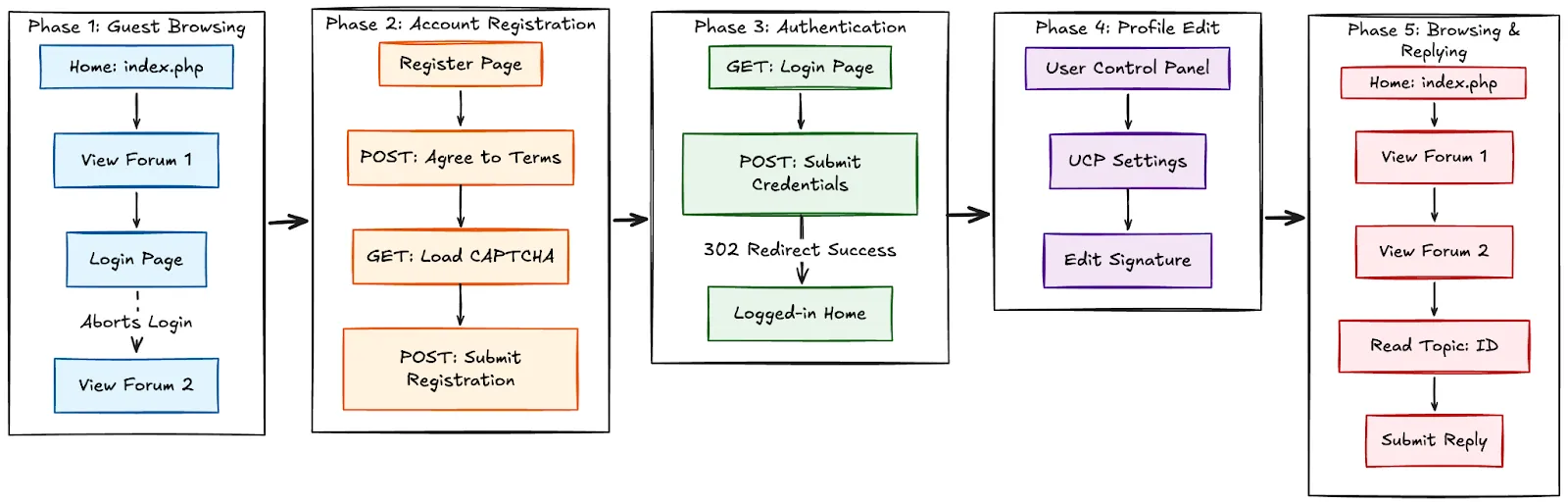
Once a campaign has been started, XRumer creates an isolated session for each forum, pulling auto-fill values from its corpus. Depending on whether the website is a forum or a simple form, it will go through different stages: either automatically filling and submitting the form or following the 6 steps to provision and post with an account.
- Guest Browsing: Fetch website, check if it’s available, and set all proper cookies.
- Account Registration: Attempt to sign up by parsing form details and checking the fields against the database of possible form values. Fill in matches and solve the necessary text- and image-based CAPTCHAs.
- Authentication: Follow the redirect flow and log in with credentials. Check the status message to see if registration has been blocked; if not, proceed to phase 4.
- Provisioning: Set up account details such as bios, profile photo, display name, and other characteristics to give the appearance of it being a real account.
- Posting: Mass-DM users on the site or post forum content, depending on the option selected in the campaign.
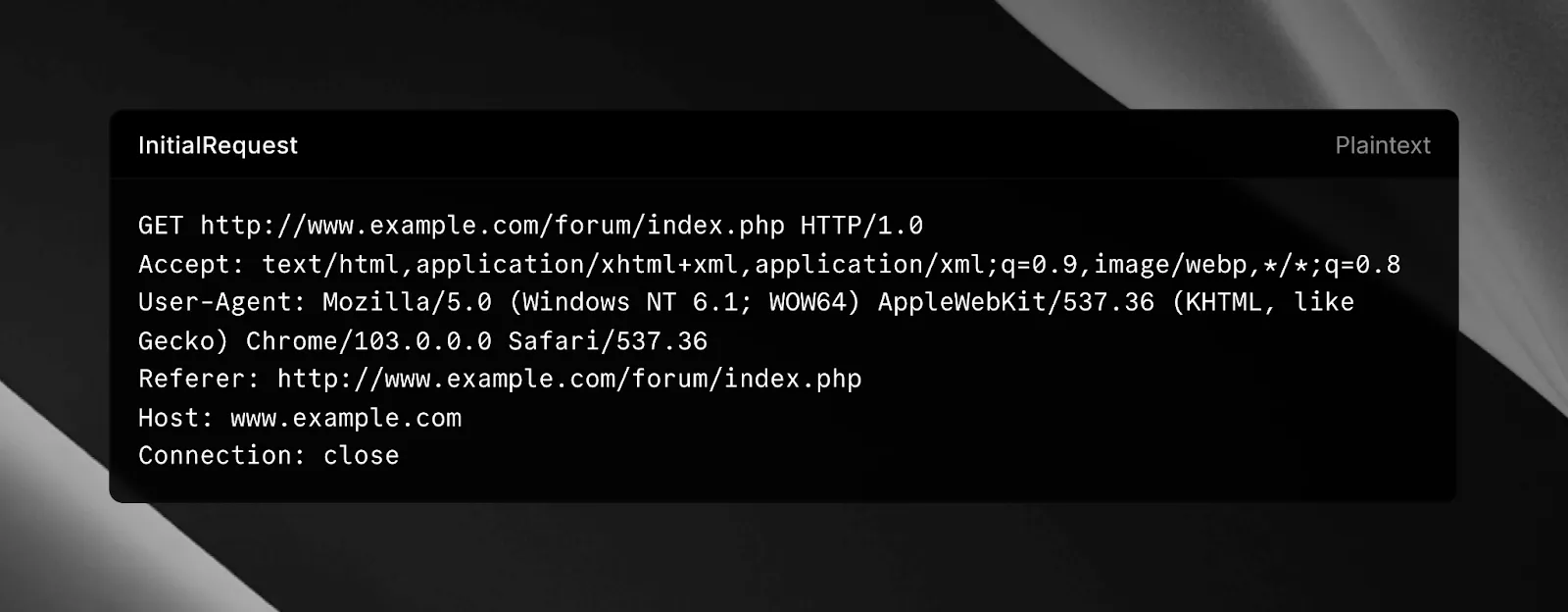
Castle’s Research Team observed XEvil initializing each session with a randomly selected user agent from the “x_user_agent” file, which contains only 31 user agents pretending to be Windows and Chromium 103.
Spammers’ Best Friend#
Castle’s Research Team purchased an expired domain from the distributed spam list provided to XRumer clients and, within the hour, observed attempts to register and post pharmaceutical-related spam to the message board.
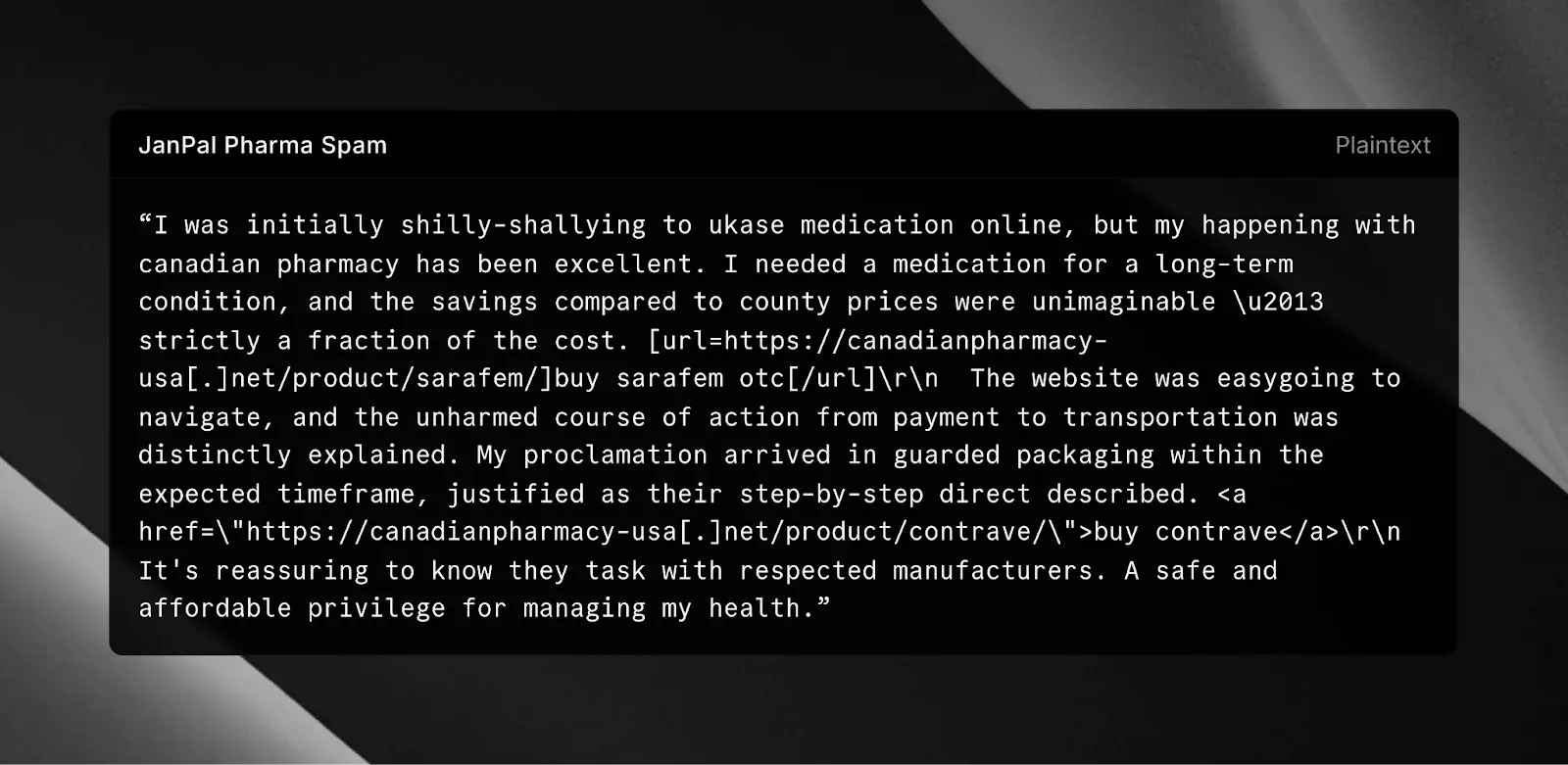
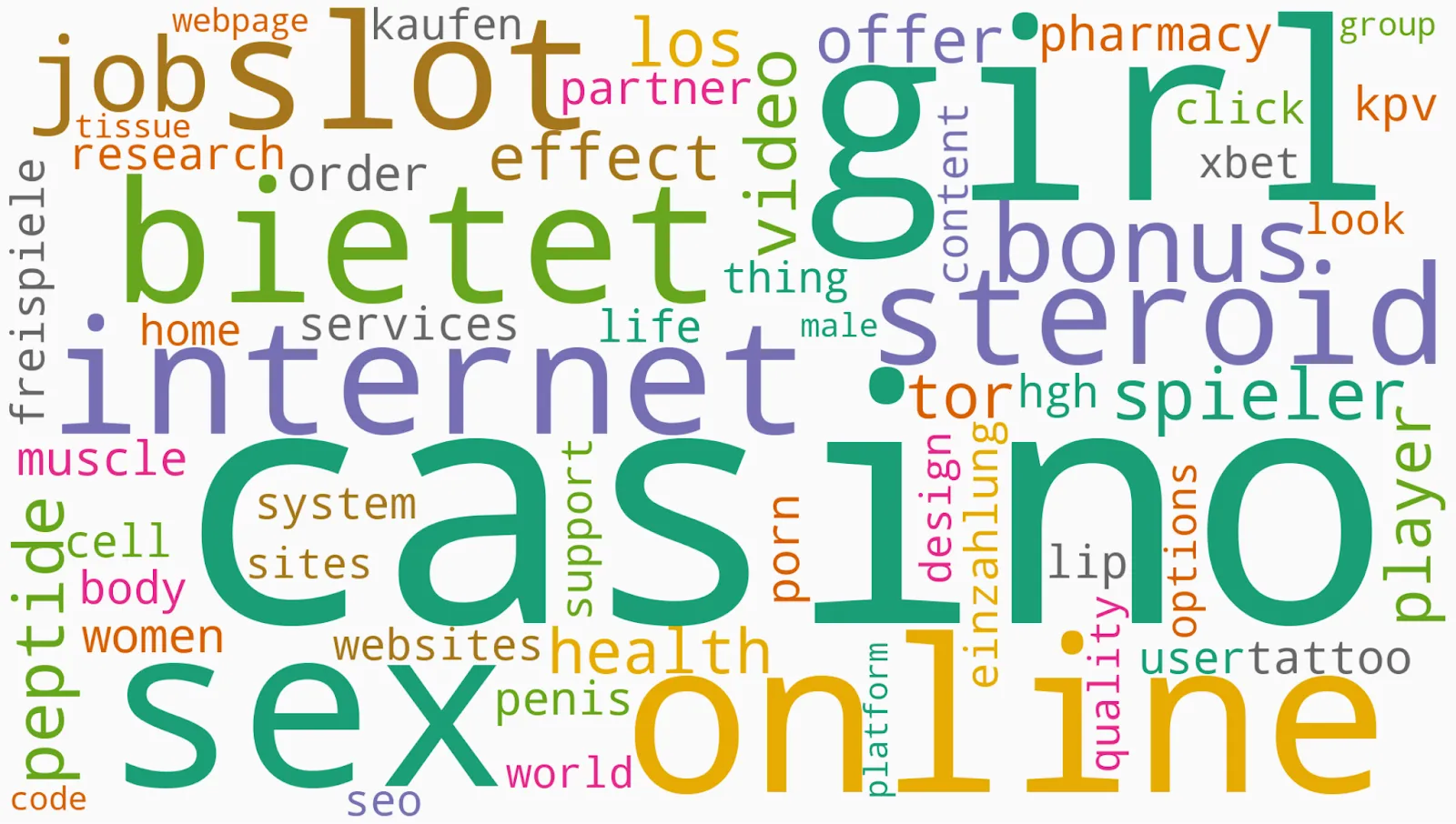
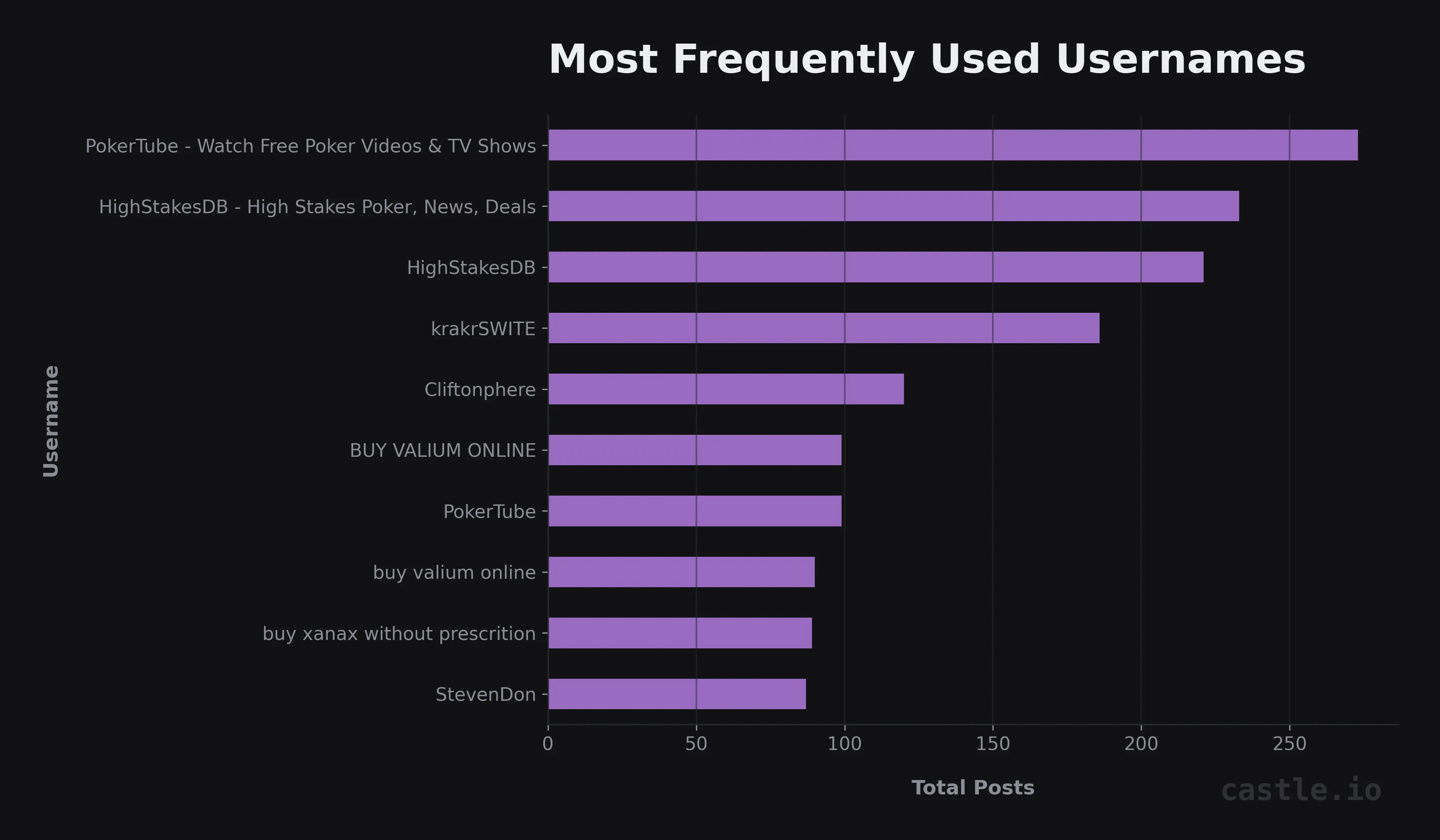
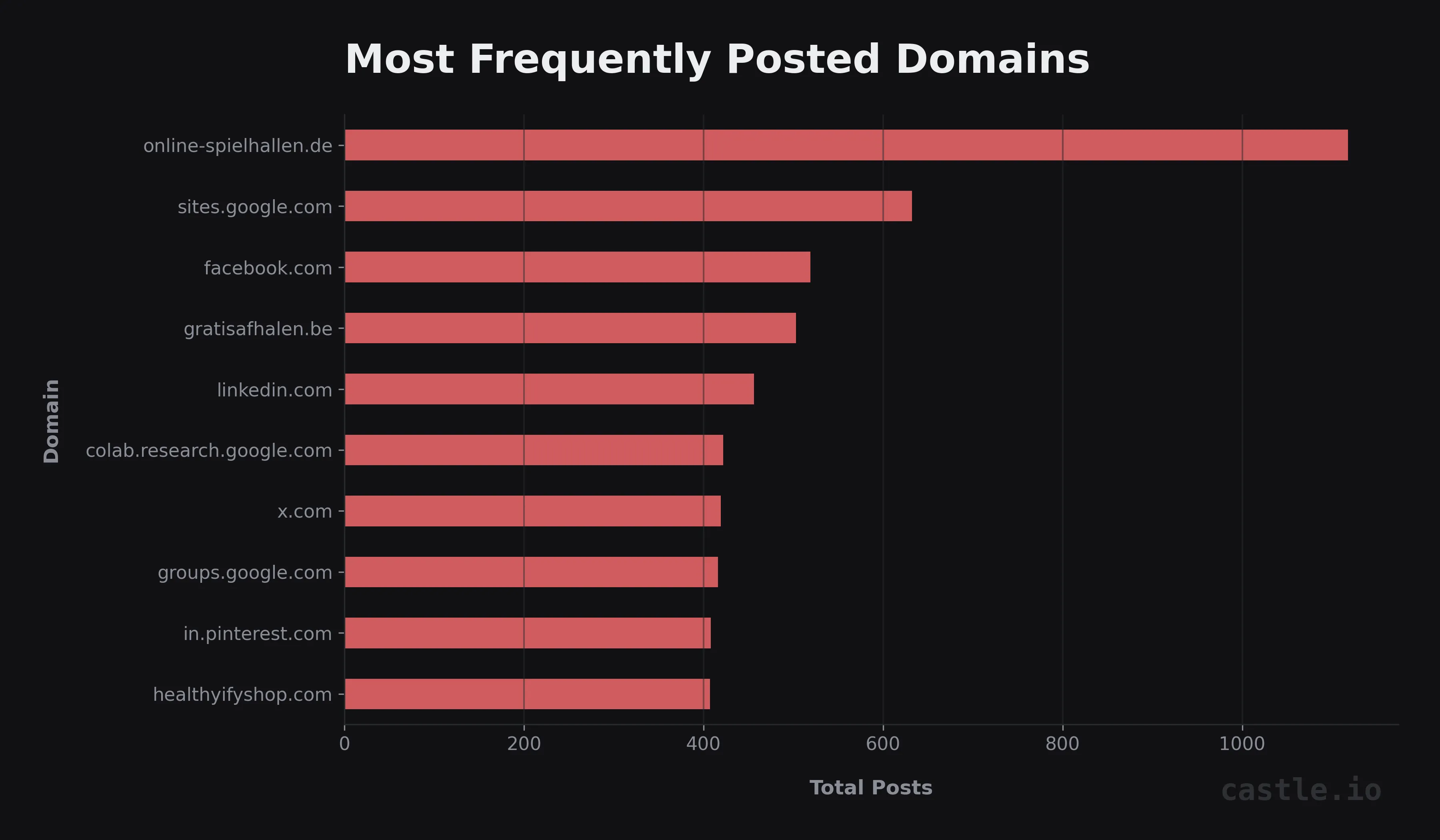
Pivoting on this spam message, Castle’s Research Team uncovered thousands of domains used by XRumer customers to push malicious ads. Upon further analysis of these posts, the following word cloud was produced, highlighting a significant portion of forum-related spam being associated with adult content such as drugs, pornography, or gambling.
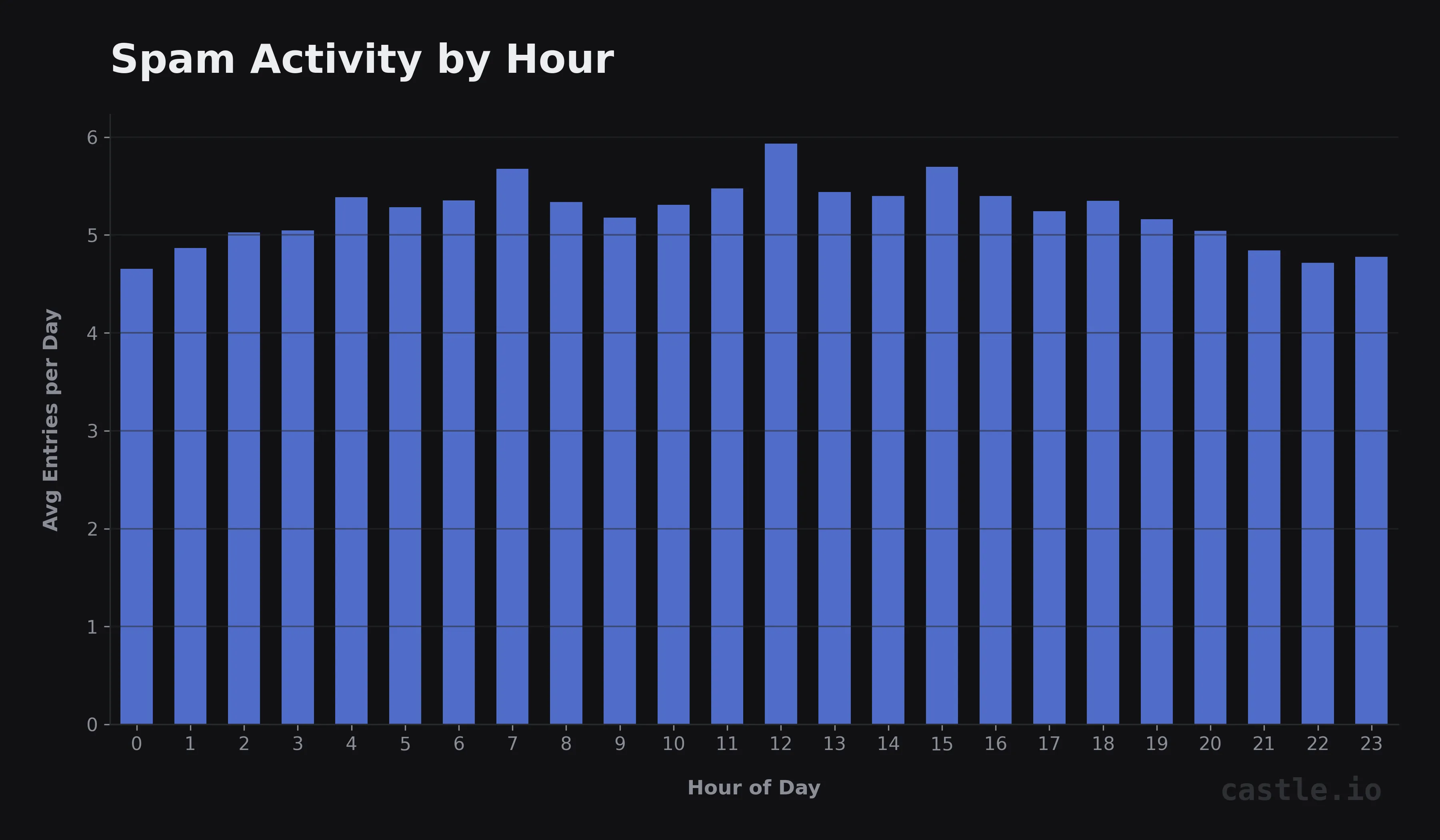
Further analysis of the dataset yields the following stats, showing a steady stream of spam throughout the day, across the week.
XEvil Analysis#
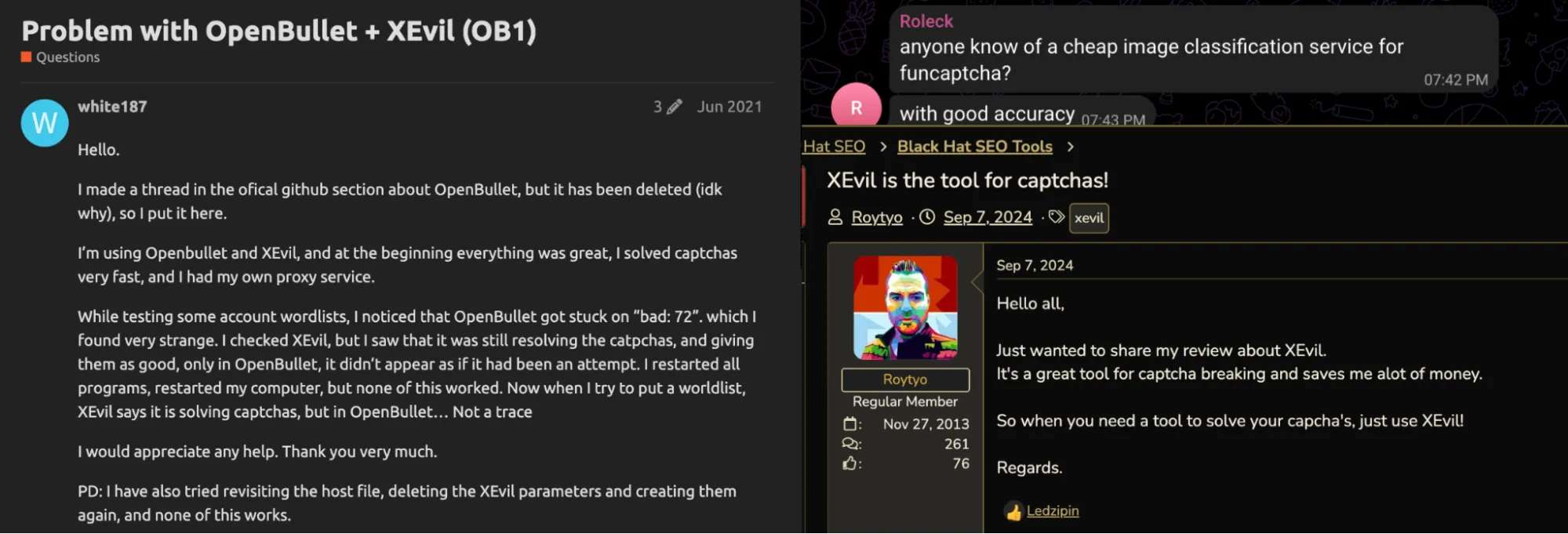
To enable tools such as XRumer to register accounts, BotmasterLabs offers a dedicated CAPTCHA-solving tool that runs locally on the operator’s machine. Castle’s Research Team notes that both individual operators of large-scale CAPTCHA-solving services, including 2Captcha, have widely adopted XEvil. Since 2017, XEvil has undergone continuous development, enabling users to solve CAPTCHA challenges from a wide range of providers, including reCAPTCHA, Arkose Labs (formerly known as FunCaptcha), and HCaptcha. As a result, XEvil has become a core component for actors engaged in large-scale botting operations.
As of this report, XEvil 6.0 supports approximately 100 types of image CAPTCHA across multiple platforms. Targets include government websites and social media services, among others.

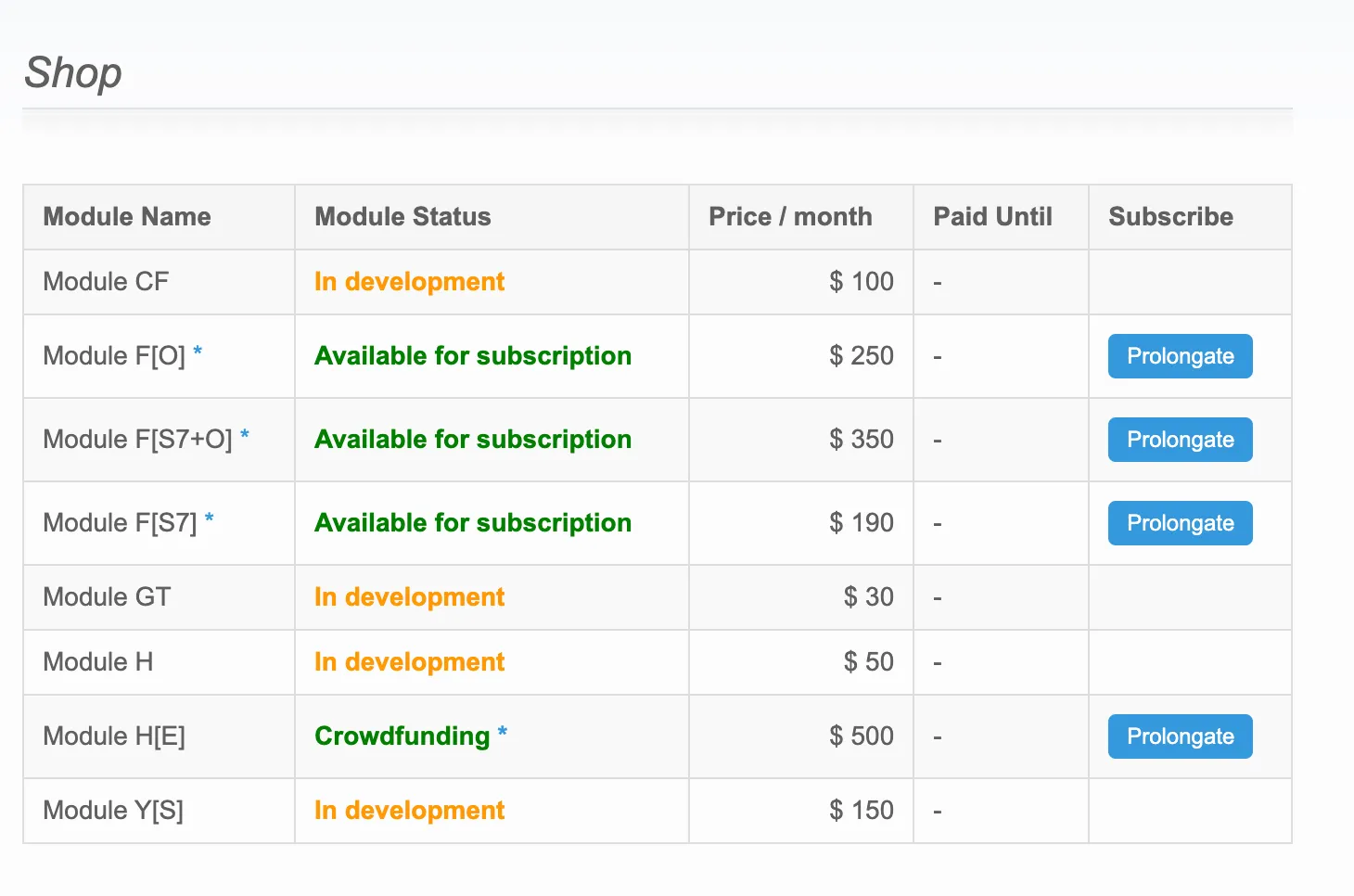
XEvil customers are able to request custom plugins via the support forum, which has increased the tool’s flexibility and adoption. Customers can also purchase model weights for specific CAPTCHA types through the XEvil marketplace, granting them access to more specialized site-specific CAPTCHAs.
XEvil’s Headless Solver#
XEvil’s HCaptcha and reCAPTCHA solving library is implemented in the rc_processor5 module, a VMP-packed Delphi binary. The core logic uses the Chromium Embedded Framework to render and execute JavaScript, while XEvil uses an almost fully static browser fingerprint to simulate legitimate traffic.
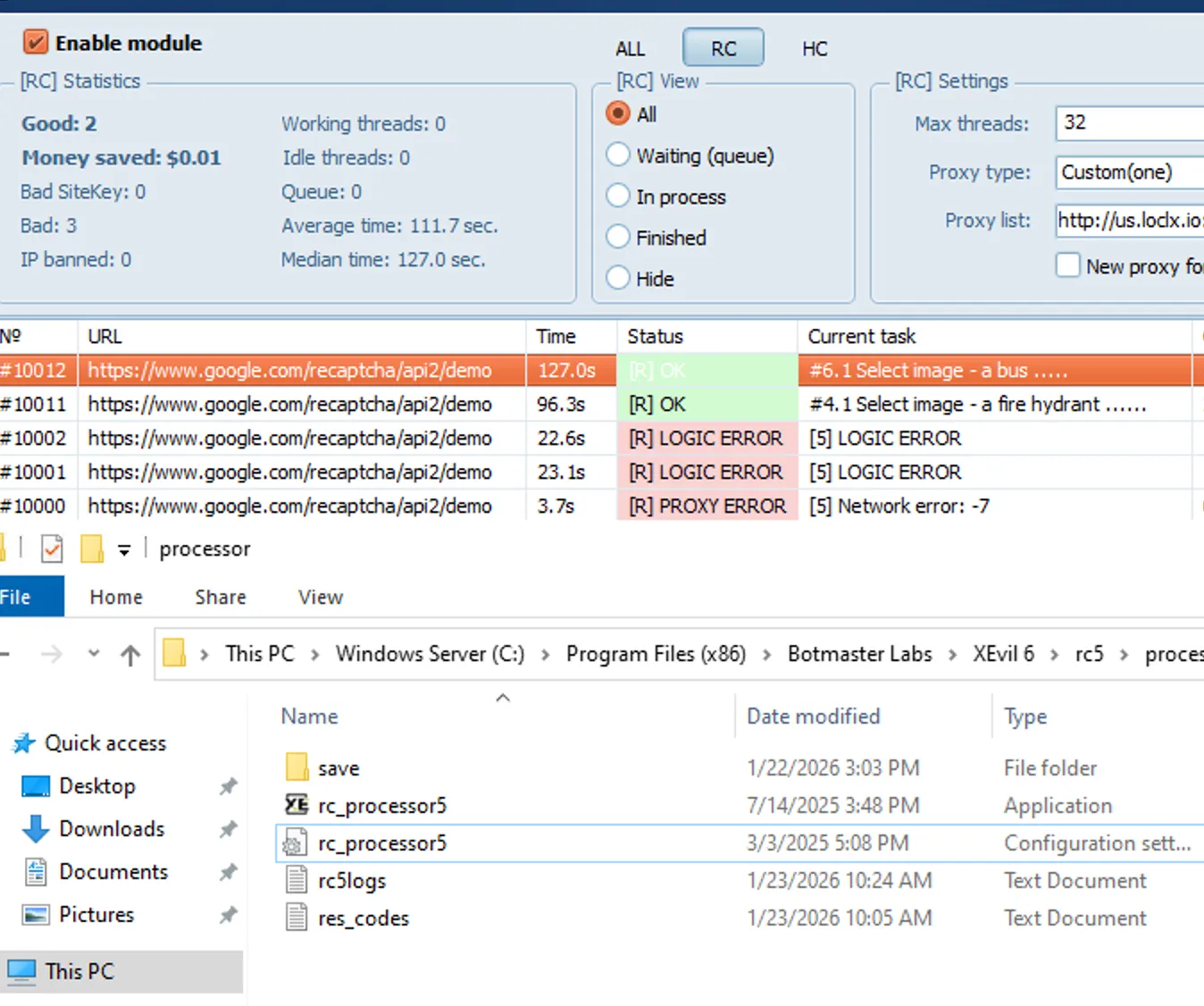
XEvil does not enforce HTTPS, which allows interception of its traffic. Castle’s Research Team was able to use this to inject custom JavaScript and identify parts of the injected browser fingerprint. XEvil notably lacks support for several standard Chromium APIs, including mediaCapabilities, clipboard, and permissions, allowing for detection due to mismatch from a standard Chrome browser. Although XEvil does allow setting a custom user agent, the implementation does not override JavaScript-specific values, further causing it to stand out.
Default XEvil user agent:
Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/133.0.0.0 Safari/537.36| JavaScript Source | Value |
|---|---|
| navigator.vendor | ”Google Inc.” |
| navigator.vendorSub | "" |
| navigator.product | ”Gecko” |
| navigator.productSub | ”20030107” |
| navigator.appName | ”Netscape” |
| navigator.appCodeName | ”Mozilla” |
| navigator.platform | ”Win32” |
| navigator.language | ”ru-RU” |
| navigator.deviceMemory | 8 |
| navigator.hardwareConcurrency | 8 |
| navigator.maxTouchPoints | 0 |
| navigator.cookieEnabled | true |
| navigator.doNotTrack | ”1” |
| navigator.onLine | true |
| navigator.pdfViewerEnabled | false |
| navigator.webdriver | false |
| screen.availTop | 0 |
| screen.availLeft | 0 |
| screen.availHeight | 1040 |
| screen.availWidth | 1920 |
| screen.width | 1920 |
| screen.height | 1080 |
| screen.colorDepth | 24 |
| screen.pixelDepth | 24 |
*Note: Both screen.innerWidth and screen.innerHeight are randomized per session and are not static.
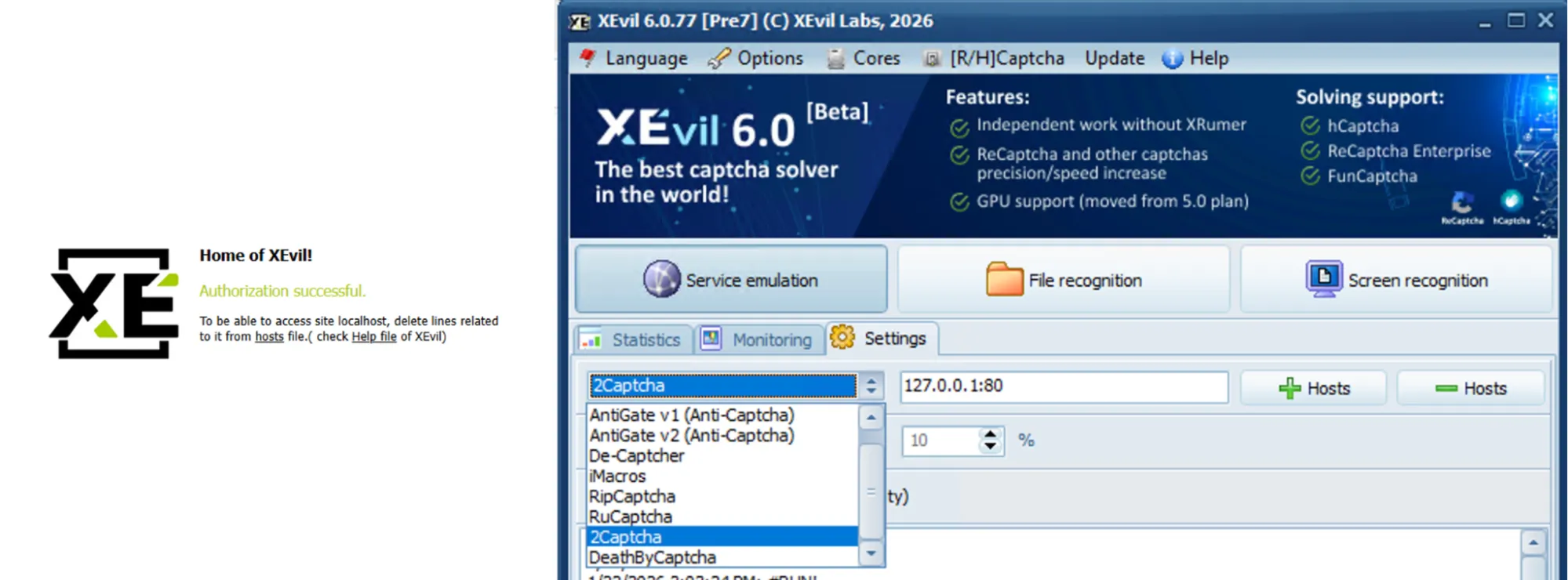
XEvil API#
XEvil’s adoption has been largely fueled by its compatibility with major CAPTCHA-solving services, which enable it to run locally and mimic APIs from services such as 2Captcha, AntiCaptcha, and Death By Captcha. This allows clients to easily swap out these larger services for XEvil, saving significant money by running it locally.
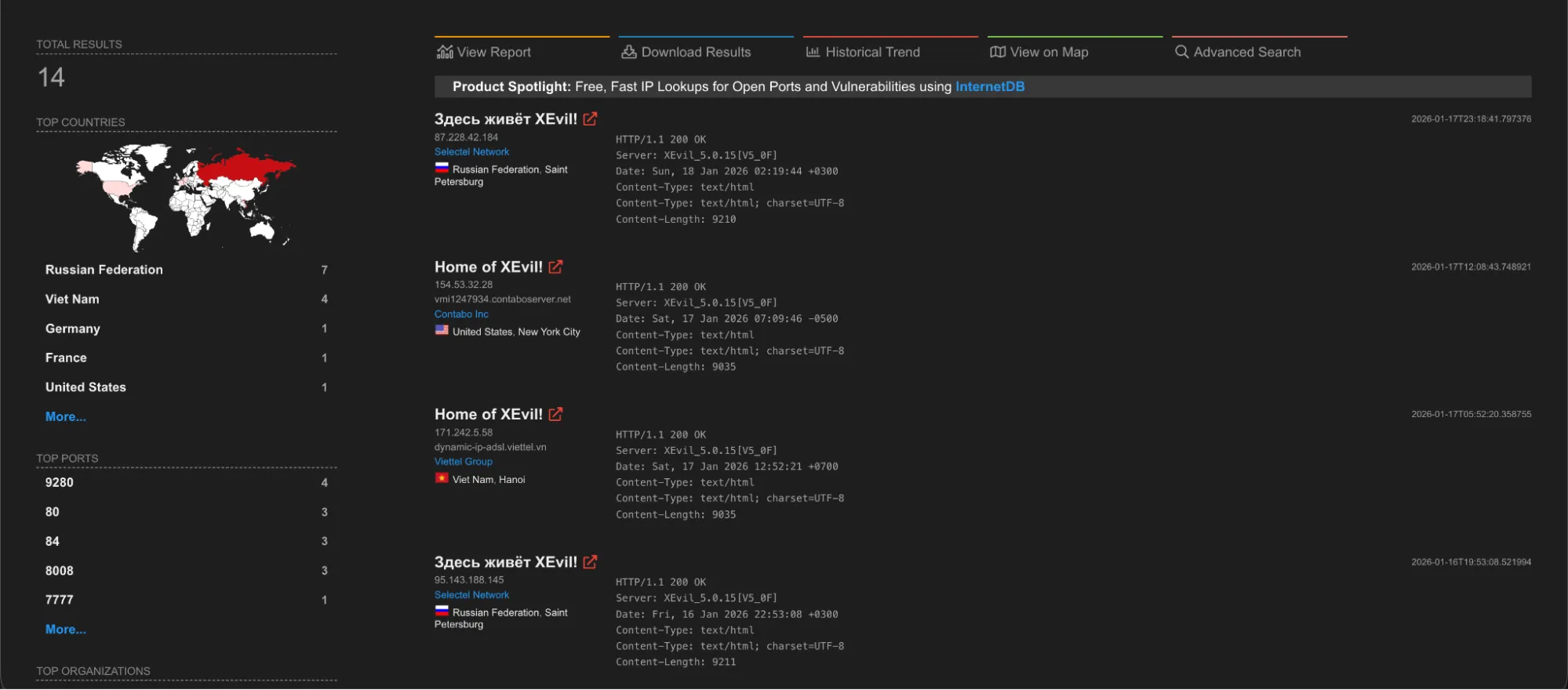
A simple Shodan query yields a number of public-facing XEvil instances in Russia, the United States, and Vietnam. While most XEvil instances use proxies by default, this is not guaranteed, and Defenders are encouraged to block these IPs.
Mitigation Strategies#
- Enforce hostname and URLs where possible: Due to XEvil and other CAPTCHA solvers not loading the page submitted in the task, in some cases it’s possible to detect a mismatch in the hostname returned by commercial CAPTCHA solvers.
- Don’t rely on image-based CAPTCHA as the only line of defense: Organizations should use additional strong JavaScript signals alongside verification methods such as email and phone to drive up costs for bot operators.
- Track challenge load times: Because the CAPTCHA is loaded externally, the time between when the user viewed the form and when the CAPTCHA was loaded might differ. Organizations should check whether the
challenge_tsis before or significantly after the page load time (window.performance); if so, the user should be blocked.
Observables#
Network Observables#
| IP Address | Hosting Org | Country | Description |
|---|---|---|---|
| 157[.]90[.]133[.]91:80 | Hetzner Online GmbH | DE | Public-facing XEvil solving instance. |
| 144[.]76[.]203[.]211:80 | Hetzner Online GmbH | DE | Public-facing XEvil solving instance. |
| 212[.]192[.]24[.]166:80 | ITSOFT LLC | RU | Public-facing XEvil solving instance. |
| 87[.]228[.]42[.]184:80 | Selectel Network | RU | Public-facing XEvil solving instance. |
| 147[.]135[.]255[.]209:80 | OVH SAS | FR | Public-facing XEvil solving instance. |
| 5[.]35[.]97[.]91:80 | JSC IOT | RU | Public-facing XEvil solving instance. |
| 212[.]192[.]24[.]133:80 | ITSOFT LLC | RU | Public-facing XEvil solving instance. |
| 109[.]194[.]67[.]56:80 | CJSC ER-Telecom Holding Tver’ branch | RU | Public-facing XEvil solving instance. |
| 87[.]228[.]42[.]186:80 | Selectel Network | RU | Public-facing XEvil solving instance. |
| 154[.]53[.]32[.]28:80 | Contabo Inc | US | Public-facing XEvil solving instance. |
| 171[.]242[.]5[.]58:80 | Viettel Group | VN | Public-facing XEvil solving instance. |
| 95[.]143[.]188[.]145:80 | Selectel Network | RU | Public-facing XEvil solving instance. |
| 117[.]1[.]131[.]151:80 | Viettel Group | VN | Public-facing XEvil solving instance. |
| Domain | Description |
|---|---|
| www[.]BotmasterLabs[.]net | BotmasterLabs English website |
| www[.]botmasterru[.]com | BotmasterLabs Russian website |
| www[.]XEvil[.]net | XEvil Website |
| botmastersupport[.]com | BotmasterLabs support forum |
| dwld[.]org | BotmasterLabs distribution website |
| fdc[.]xchecker[.]net | XRumer Proxy Checking Server |
File Observables#
| Filename | SHA-256 Hash | Description |
|---|---|---|
| XEvil_5.0.15.866_Setup(RC_Fixed2024).exe | d648a2fe16caa290c3ead0b28fc4e6592f8ef5b12eff363dceebcc056c6408a3 | XEvil 5.0 Setup File |
| rc_processor5.exe | 20211e4db11fec6c0988224f376dacda8a1ca6e78f33c2151d62c2bef9e5919b | XEvil 5.0 CAPTCHA Solver Module |
| XEvil_6.0.77.1176_Setup.exe | 4d24ee0dae17cb1702ac973430549b3f722c7da722631b71ce3bface4a621a6b | XEvil 6.0 Setup File |
| rc_processor5.exe | 74a3a45e0e5358893d4e5f84e24d7168b4f243629ea2514bebe5c9b6b384cf48 | XEvil 6.0 CAPTCHA Solver Module |
Future Outlook#
BotmasterLabs continues to actively develop XRumer and XEvil, with their next major release anticipated in the coming months. XRumer has significantly improved its auto-generated responses by integrating support for commercial machine learning models. Additionally, XEvil has undergone a major overhaul and is expected to introduce support for reCAPTCHA Enterprise, Cloudflare, SmartCaptcha, and GeeTest. Castle’s Research Team assesses that both XEvil and XRumer will continue to support low-level cybercrime.
This trend indicates a broader shift within the automated abuse landscape. Threat actors are increasingly weaponizing artificial intelligence to bypass traditional security controls at scale. As machine learning models become more accessible and cost-effective for cybercriminals, the overall efficacy of image-based CAPTCHA is expected to continue to decline.
Consequently, organizations should pivot away from relying solely on static visual challenges. Defenders are advised to adopt multi-layered, behavior-based detection strategies. Implementing advanced device fingerprinting, biometric interaction analysis, and continuous session monitoring to counter automated threats such as XEvil and XRumer.